Python is a highly popular programming language in the realm of cybersecurity due to its versatility and user-friendliness. This article delves into why Python is crucial for cybersecurity, highlighting its adaptability, ease of use, and the myriad of cybersecurity applications that can be developed with it.
Introduction
In the world of cybersecurity, Python stands out as a vital tool. This programming language is known for its versatility, simplicity, and extensive library support, which are all essential for creating complex cybersecurity applications. This article will discuss why Python is important for cybersecurity and provide practical examples of its application in developing security tools and solutions.
Why Python is Ideal for Cybersecurity
Python’s suitability for cybersecurity stems from its simplicity and flexibility. Its straightforward syntax makes it accessible to developers, even those with minimal programming experience. Additionally, Python’s extensive library ecosystem simplifies the creation of sophisticated applications, including cybersecurity tools.
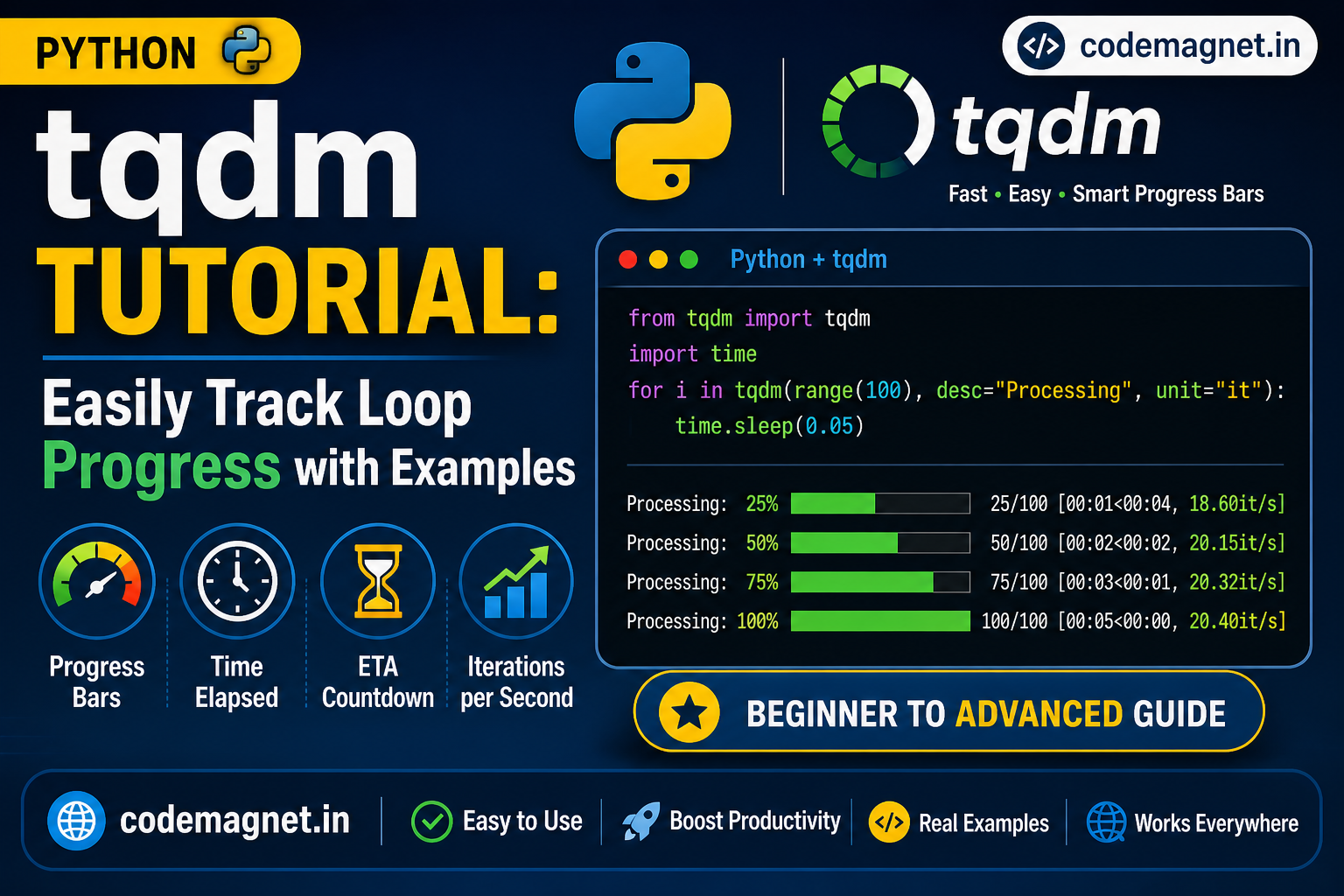
A significant advantage of Python in cybersecurity is its automation capabilities. Many cybersecurity tasks, such as threat detection and data analysis, involve processing vast amounts of data. Python excels in automating these tasks, making data analysis more efficient and timely. Moreover, Python’s data visualization libraries enable the creation of graphical data representations, helping identify patterns and trends.
Python’s ability to integrate with various tools and technologies further enhances its utility in cybersecurity. It supports numerous libraries and frameworks that facilitate integration with other security tools like network scanners and intrusion detection systems, enabling comprehensive security solutions within an organization’s infrastructure.
The active Python community is another asset, providing a wealth of resources such as tutorials, forums, and open-source libraries. This community support aids developers in learning and applying Python to cybersecurity tasks effectively.
Examples of Cybersecurity Applications Using Python
- Network Scanning and Analysis: Network scanning involves identifying and analyzing devices and services on a network. Python, with libraries like Scapy and Nmap, allows for detailed network packet manipulation and scanning, aiding in vulnerability identification and network traffic analysis.
Install Scapy
First, you need to install Scapy. You can do this using pip:
pip install scapy
This example performs an ARP scan to identify devices on the local network.
from scapy.all import ARP, Ether, srp
def arp_scan(ip_range):
# Create an ARP request packet
arp_request = ARP(pdst=ip_range)
# Create an Ethernet frame
ether = Ether(dst="ff:ff:ff:ff:ff:ff")
# Combine the Ethernet frame and ARP request packet
arp_request_broadcast = ether/arp_request
# Send the packet and capture the response
answered, unanswered = srp(arp_request_broadcast, timeout=2, verbose=False)
# Parse the response
devices = []
for sent, received in answered:
devices.append({'ip': received.psrc, 'mac': received.hwsrc})
return devices
# Specify the IP range (adjust according to your network)
ip_range = "192.168.1.0/24"
# Perform the ARP scan
devices = arp_scan(ip_range)
# Print the results
print("Devices found on the network:")
for device in devices:
print(f"IP: {device['ip']}, MAC: {device['mac']}")
Using Nmap for Network Scanning
pip install python-nmap
import nmap
def nmap_scan(ip_range):
# Create an Nmap PortScanner object
nm = nmap.PortScanner()
# Perform the scan
scan_result = nm.scan(ip_range, arguments='-sP -n')
# Parse the result
devices = []
for host in nm.all_hosts():
device_info = {
'ip': host,
'state': nm[host].state(),
'hostnames': nm[host].hostnames(),
'all_protocols': nm[host].all_protocols(),
}
# Gather port information if any
for proto in nm[host].all_protocols():
lport = nm[host][proto].keys()
device_info[proto] = [{'port': port, 'state': nm[host][proto][port]['state']} for port in lport]
devices.append(device_info)
return devices
# Specify the IP range (adjust according to your network)
ip_range = "192.168.1.0/24"
# Perform the Nmap scan
devices = nmap_scan(ip_range)
# Print the results
print("Devices found on the network:")
for device in devices:
print(f"IP: {device['ip']}, State: {device['state']}")
for proto in device['all_protocols']:
for port_info in device[proto]:
print(f" - {proto.upper()} Port {port_info['port']}: {port_info['state']}")
Summary
- Scapy: Provides low-level access to network packets and allows detailed packet manipulation and analysis. The example shows how to perform an ARP scan to identify devices on a local network.
- Nmap with
python-nmap: Leverages the power of Nmap for network scanning to identify hosts and open ports. The example demonstrates a basic network scan to detect active devices and their open ports.
2. Intrusion Detection and Prevention: Intrusion detection involves identifying unauthorized access or attacks on a network. Python’s libraries, such as Scapy for network packet analysis and Scikit-learn for anomaly detection, enable the creation of effective intrusion detection and prevention systems.
3. Malware Analysis: Malware analysis involves understanding the behavior of malicious software. Python’s scripting capabilities, along with libraries for file and network traffic analysis, make it suitable for automating malware analysis and developing custom analysis tools.
4. Penetration Testing: Penetration testing, or ethical hacking, involves simulating attacks to identify vulnerabilities. Python is preferred for this due to its libraries like Scapy for network tasks and Metasploit for exploit execution, allowing for efficient penetration testing automation.
5. Web Application Security: Python aids in securing web applications through automated scanning, vulnerability analysis, and penetration testing. Libraries like Scrapy, BeautifulSoup, and Requests are used for these tasks, enhancing web application security.
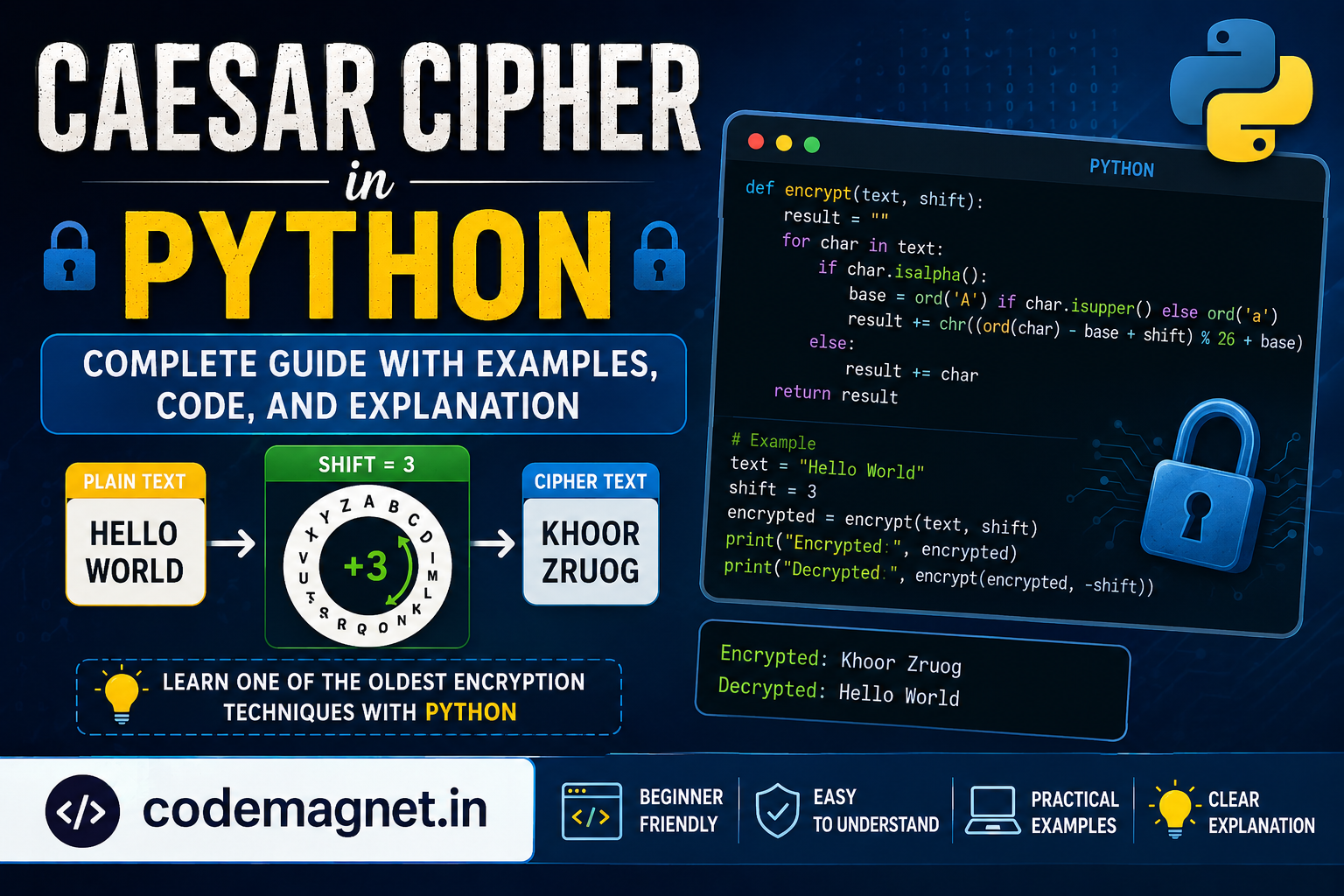
- Cryptography: Python simplifies cryptographic tasks such as encryption, decryption, and digital signatures. Libraries like PyCrypto and the built-in SSL library support various cryptographic algorithms, making Python suitable for secure communication and data storage.
- Data Visualization: Python’s libraries like Matplotlib, Seaborn, and Plotly are used for creating visual representations of data, which is crucial for identifying cybersecurity threats and trends. These visualizations help in quick threat identification and response.
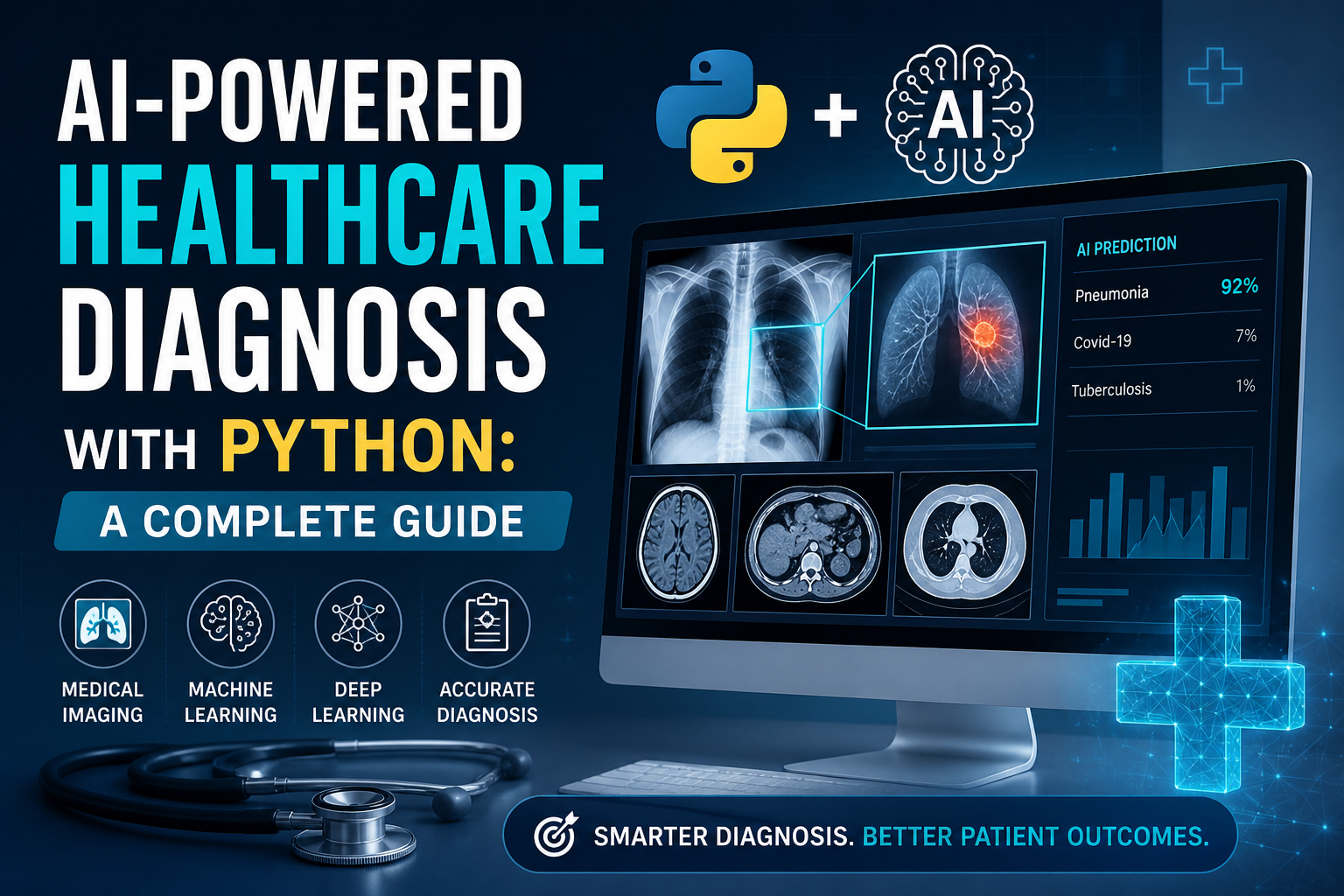
- Machine Learning: In cybersecurity, machine learning (ML) is used for anomaly detection, malware classification, and phishing detection. Python, with libraries like Scikit-learn, TensorFlow, and Keras, is widely used for developing ML models to enhance cybersecurity measures.
- IoT Security: Python is employed in IoT security to monitor network traffic, detect anomalies, and identify potential threats. Libraries and tools like PyIoT are used for vulnerability assessments and security analysis of IoT devices.
Python Libraries for Cybersecurity
- Scapy: For network packet manipulation and analysis.
- Pyshark: A wrapper for Wireshark, used for network traffic analysis.
- Yara: For malware identification and classification.
- Requests: For making HTTP requests, useful in web application testing.
- PyCrypto: For cryptographic operations like encryption and decryption.
- Matplotlib: For data visualization.
- Scikit-learn: For machine learning applications in threat detection.
- PyIoT: For IoT security analysis.
Advantages of Python in Cybersecurity
- Ease of Learning and Use: Python’s simple syntax makes it accessible to beginners and experienced developers alike.
- Community Support and Libraries: A large, active community and extensive libraries provide ample resources and support.
- Flexibility and Customizability: Python’s versatility allows for the creation of customized solutions to meet specific cybersecurity needs.
In summary, Python’s simplicity, flexibility, extensive library support, and active community make it an indispensable tool in the field of cybersecurity, enabling the development of effective and efficient security solutions.



Leave a Reply